Ransomware is an epidemic today based on an insidious piece of malware that cyber-criminals use to extort money from you by holding your computer or computer files for ransom, demanding payment from you to get them back.
Unfortunately, Ransomware is quickly becoming an increasingly popular way for malware authors to extort money from companies and consumers alike. Should this trend be allowed to continue, Ransomware will soon affect IoT devices, cars and ICS and SCADA systems as well as just computer endpoints. There are several ways Ransomware can get onto someone’s computer but most result from a social engineering tactic or using software vulnerabilities to silently install on a victim’s machine.
For a long time now, malware authors have sent waves of spam emails targeting various groups. There is no geographical limit on who can be affected, and while initially, emails were targeting individual end-users, then small to medium businesses, now the enterprise is the ripe target.
In addition to phishing and spear-phishing social engineering, Ransomware also spreads via remote desktop ports. Ransomware also affects files that are accessible on mapped drives including external hard drives such as USB thumb drives, external drives, or folders on the network or in the Cloud. If you have a OneDrive folder on your computer, those files can be affected and then synchronized with the Cloud versions.
No one can say with any accurate certainty how much malware of this type is in the wild. As much of it exists in unopened emails and many infections go unreported, it is difficult to tell.
The impact on those who were affected is that data files have been encrypted and the end-user is forced to decide, based on a ticking clock, whether to pay the ransom or lose the data forever. Files affected are typically popular data formats such as Office files, music, PDF and other popular data files. More sophisticated strains remove computer “shadow copies” which would otherwise allow the user to revert to an earlier point in time. In addition, computer “restore points” are being destroyed as well as backup files that are accessible. The way the process is managed by the criminal is they have a Command and Control server that holds the private key for the user’s files. They apply a timer to the destruction of the private key, and the demands and countdown timer are displayed on the user’s screen with a warning that the private key will be destroyed at the end of the countdown unless the ransom is paid. The files themselves continue to exist on the computer, but they are encrypted, and inaccessible even to brute force.
In many cases, the end-user simply pays the ransom, seeing no way out. The FBI recommends against paying the ransom. By paying the ransom, you are funding further activity of this kind and there is no guarantee that you will get any of your files back. In addition, the cyber-security industry is getting better at dealing with Ransomware. At least one major anti-malware vendor has released a “decryptor” product in the past week. It remains to be seen, however, just how effective this tool will be.
What you should do now
There are multiple perspectives to be considered. The individual wants their files back. At the company level, they want the files and assets to be protected. At the enterprise level, they want all of the above and must be able to demonstrate the performance of due diligence in preventing others from becoming infected by anything that was deployed or sent from the company to protect them from the mass torts that will inevitably strike in the not so distant future.
Generally speaking, once encrypted, it is unlikely the files themselves can be unencrypted. The best tactic, therefore, is prevention.
Back up your data
The best thing you can do is to perform regular backups to offline media, keeping multiple versions of the files. With offline media, such as a backup service, tape, or other media that allows for monthly backups, you can always go back to old versions of files. Also, make sure you are backing up all data files – some may be on USB drives or mapped drives or USB keys. As long as the malware can access the files with write-level access, they can be encrypted and held for ransom.
Education and Awareness
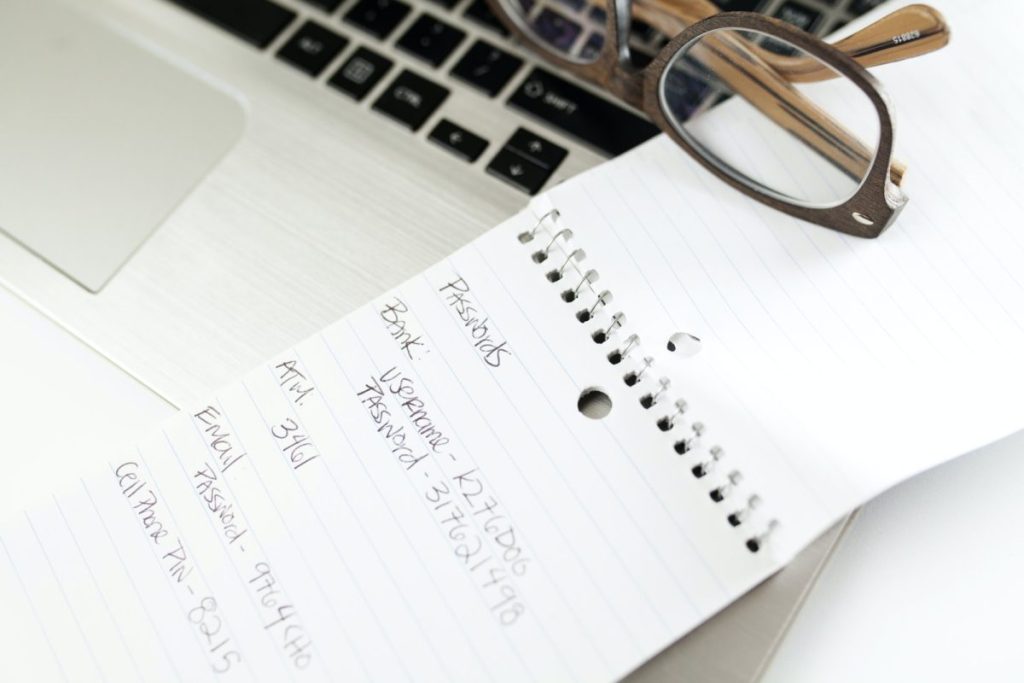
A critical component in the process of prevention of Ransomware infection is making your end-users and personnel aware of the attack vectors, specifically SPAM, phishing and spear-phishing. Almost all Ransomware attacks succeed because an end-user clicks on a link that appears innocuous or opens an attachment that looks like it came from a known individual. By making staff aware and educating them on these risks, they can become a critical line of defence against this insidious threat.
Show hidden file extensions
Typically Windows hides known file extensions. If you enable the ability to see all file extensions in email and on your file system, you can more easily detect suspicious malware code files masquerading as friendly documents.
Filter out executable files in email
If your gateway mail scanner has the ability to filter files by extension, you may want to deny email messages sent with *.exe file attachments. Use a trusted cloud service to send or receive *.exe files.
Disable files from executing from Temporary file folders
First, you should allow hidden files and folders to be displayed in Explorer so you can see the appdata and programdata folders.
Your anti-malware software allows you to create rules to prevent executables from running from within your profile’s appdata and local folders as well as the computer’s programdata folder. Exclusions can be set for legitimate programs.
Disable RDP
If it is practical to do so, disable RDP (remote desktop protocol) on ripe targets such as servers, or block them from Internet access, forcing them through a VPN or other secure route. Some versions of Ransomware take advantage of exploits that can deploy Ransomware on a target RDP-enabled system. There are several TechNet articles detailing how to disable RDP.
Patch and update everything
It is critical that you stay current with your Windows updates as well as antivirus updates to prevent a Ransomware exploit. Not as obvious is that it is just as important to stay current with all Adobe software and Java. Remember, your security is only as good as your weakest link.
Use a layered approach to endpoint protection
It is not the intent of this article to endorse anyone endpoint product over another, but rather to recommend a methodology that the industry is quickly adopting. You must understand that Ransomware as a form of malware, feeds off of weak endpoint security. If you strengthen endpoint security then Ransomware will not proliferate as easily. A report released by the Institute for Critical Infrastructure Technology (ICIT) recommends a layered approach, focusing on behaviour-based, heuristic monitoring to prevent the act of non-interactive encryption of files (which is what Ransomware does), and at the same time run a security suite or endpoint anti-malware that is known to detect and stop Ransomware. It is important to understand that both are necessary because while many anti-virus programs will detect known strains of this nasty Trojan, unknown zero-day strains will need to be stopped by recognizing their behaviour of encrypting, changing the wallpaper and communicating through the firewall to their Command and Control centre.
What you Should do if you think you are infected
Disconnect from any WiFi or corporate network immediately. You might be able to stop communication with the Command and Control server before it finishes encrypting your files. You may also stop Ransomware on your computer from encrypting files on network drives.
Use system restore to get back to a known clean state
If you have system restore enabled on your Windows machine, you may be able to take your system back to an earlier restore point. This will only work if the strain of Ransomware you have has not yet destroyed your restore points.
Boot to a boot disk and run your antivirus software
If you boot to a boot disk, none of the services in the registry will be able to start, including the Ransomware agent. You may be able to use your antivirus program to remove the agent.
Advanced users may be able to do more
Ransomware embeds executables in your profile’s Appdata folder. In addition, entries in the Run and Runonce keys in the registry automatically start the Ransomware agent when your OS boots. An Advanced User should be able to
- Run a thorough endpoint antivirus scan to remove the Ransomware installer
- Start the computer in Safe Mode with no Ransomware running, or terminate the service.
- Delete the encryptor programs
- Restore encrypted files from offline backups.
- Install layered endpoint protection including both behavioural and signature-based protection to prevent re-infection.